Media Summary: Don't miss out on the latest videos, hit the bell! And subscribe to my new channel! In this video, you'll learn how to protect ... Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... Understanding how we lose out passwords, helps us understand how to protect our online accounts #
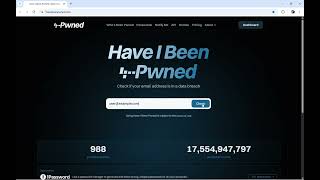
Where Hackers Get Your Leaked Data - Detailed Analysis & Overview
Don't miss out on the latest videos, hit the bell! And subscribe to my new channel! In this video, you'll learn how to protect ... Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... Understanding how we lose out passwords, helps us understand how to protect our online accounts # Aadhaar का डेटा Dark Web पर बिक रहा है The **Aadhaar Data Leak** has once again exposed how vulnerable our digital ... IP reputation check tools are essential in the toolbox of a cybersecurity analyst. They serve to evaluate the trustworthiness of an IP ...