Media Summary: Mia Epner, who works on security for a US national intelligence agency, explains how cryptography allows for the secure transfer ... In this easy to understand video, we break down what The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ...
What Is Encryption - Detailed Analysis & Overview
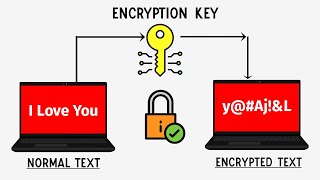
Mia Epner, who works on security for a US national intelligence agency, explains how cryptography allows for the secure transfer ... In this easy to understand video, we break down what The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... Cryptography is scary. In this tutorial, we get hands-on with Node.js to learn how common crypto concepts work, like hashing, ... WhatsApp, iMessage, Android Messages and Signal all use the super-secure system called end-to-end Welcome to our latest term definition video: "
To help councils tackle growing cyber threats, the Local Government Association has released explainer animations on cyber ... IITK - Professional Certificate Program in Blockchain (India Only) ... How hard is it to find a 256-bit hash just by guessing and checking? Help fund future projects: ... There is a lot of data in today's world constantly being sent to and from or even sitting on our hard drives but what stops someone ... Namaskaar Dosto, is video mein maine aapko How does data travel around the internet without becoming publicly visible?
This lesson will help CISSP candidates (and hopefully everyone else) to fully understand what