Media Summary: Jump into Pay What You Can training for more free Can Microsoft 365 provide Cyber Awareness training for all of your Looking for a Job? I Give You the 5 Best Ways to Find a Job in Cyber: I know many of you are struggling. I see your posts. I talk to ...
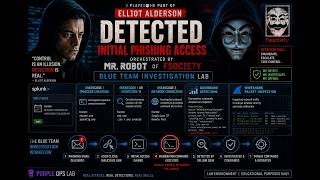
Cybersecurity Lab Simulation Red Team Phishing Attack Walkthrough - Detailed Analysis & Overview
Jump into Pay What You Can training for more free Can Microsoft 365 provide Cyber Awareness training for all of your Looking for a Job? I Give You the 5 Best Ways to Find a Job in Cyber: I know many of you are struggling. I see your posts. I talk to ... Social engineering is one of the most powerful Room Link: In this video will use Elastic to solve the scenario.