Media Summary: In this video, you'll get a comprehensive introduction to the Vigenere Cipher. Whether you're a beginner or looking to refine your ... An art installation known as Kryptos was inaugurated at CIA headquarters in late 1990. The main attraction was a curved copper ... Former covert CIA intelligence officer Andrew Bustamante teaches you how to use a basic alphabet cipher to encode and decode ...
What Does L194 Mean Deciphering The Code Behind This Cryptic Term - Detailed Analysis & Overview
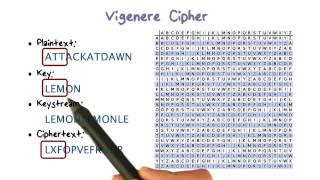
In this video, you'll get a comprehensive introduction to the Vigenere Cipher. Whether you're a beginner or looking to refine your ... An art installation known as Kryptos was inaugurated at CIA headquarters in late 1990. The main attraction was a curved copper ... Former covert CIA intelligence officer Andrew Bustamante teaches you how to use a basic alphabet cipher to encode and decode ... In this video, we investigate the Pigpen cipher, including how to encrypt and In this session, we review FHIR's three datatypes for coded data: * Hidden messages, and how we uncover them. A quick look at cryptography, cryptanalysis and decipherment. The 2014 film, The ...
This video explains how to use my online shift cipher tool. This video was produced for Lesson 5 of Journey of the Soul, a course by the Rohr Jewish Learning Institute. --- Subscribe to our ... This video shows the process (thoroughly) of how to find the key when you don't have it. English alphabet frequencies: ... I really like the cryptography and decided to create a brief history of ciphers throughout the history. I recently saw videos like, "Top ... BarrySploit walks through how to process and interpret forensic artifacts using Eric Zimmerman's tools, followed by a live ... Why some numbers just dont work when you're creating error proof
Welcome to my new series here on Physics Teacher - Summing up why Hamming's error correcting In this episode, Fiona Connolly, Platform Innovation and Automation Scientist previously at bit.bio, explains how deterministic ...