Media Summary: Join the Academy: ☕☕ COFFEE and MERCH: . The exact same security tips get repeated all the time. Of COURSE you want strong passwords and 2FA, but what are some easy ... In a time where companies, celebrities, and even governments are coming under cyber-attacks, getting
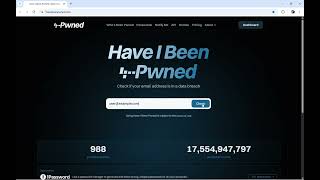
How Hackers Exploit Your Emails Protect Yourself Today - Detailed Analysis & Overview
Join the Academy: ☕☕ COFFEE and MERCH: . The exact same security tips get repeated all the time. Of COURSE you want strong passwords and 2FA, but what are some easy ... In a time where companies, celebrities, and even governments are coming under cyber-attacks, getting Want to uncover the latest insights on ransomware, dark web threats, and AI risks? Read the 2024 Threat Intelligence Index ... Identity theft can happen in minutes through data breaches, phishing, social engineering, and malware. In this video, we explain ... Phishing attacks are on the rise, especially with the ledger
In this video, we dive into the world of cybersecurity to show you how Ransomware is one of the most dangerous cyber attacks